macOS High Sierra – make sure your system is safe
updated for ClamAV release 0.100.0
If you want to make sure that your macOS High Sierra is clean (when it comes to malicious software) you can use free tool (free as in beer and free as in speech – at the same time) called ClamAV.
You can get it various ways. You can download it’s commercial version from AppStore – as paid release, you can install it using brew, download binary from some place where you have no idea what’s really inside, You can instal macOS Server (ClamAV comes bundled with it), etc.
However, you can also build it by yourself. Directly from sources. It’s a pain in a neck, I know, but you can be sure of what you are actually running. And, you will learn that zlib’s library author is a really brainy person. Go ahead, look for yourself in Wikipedia.
Anyway. Let’s start. Estimated time to complete (depending on your system configuration) – 1h-2h.
I suggest to create some place, where you can put all sources and binaries. I suggest following approach
mkdir -p $HOME/opt/src mkdir -p $HOME/opt/usr/local
In each step, we will download source codes of given tool into
$HOME/opt/src
and then, use
./configure --prefix=$HOME/opt/usr/local/$TOOL_NAME
to install them inside $HOME/opt.
1. You need PCRE – Perl Compatible Regular Expressions
cd $HOME/opt/src curl -O ftp://ftp.csx.cam.ac.uk/pub/software/programming/pcre/pcre2-10.30.tar.gz tar zxf pcre2-10.30.tar.gz cd pcre2-10.30 ./configure --prefix=$HOME//opt/usr/local/pcre2 make make install # You can also run `make check` before installing PCRE, but you may need to apply path # source: https://bugs.exim.org/attachment.cgi?id=1031&action=diff # # To apply it, simply put patch content inside file RunGrepTest.fix # # # --- 8< --- CUT HERE --- 8< --- CUT HERE --- 8< --- CUT HERE --- 8< --- --- RunGrepTest 2017-07-18 18:47:56.000000000 +0200 +++ RunGrepTest.fix 2018-01-07 20:00:40.000000000 +0100 @@ -681,7 +681,7 @@ # works. printf "%c--------------------------- Test N7 ------------------------------\r\n" - >>testtrygrep -if [ `uname` != "SunOS" ] ; then +if [ `uname` != "Darwin" ] ; then printf "abc\0def" >testNinputgrep $valgrind $vjs $pcre2grep -na --newline=nul "^(abc|def)" testNinputgrep | sed 's/\x00/ZERO/' >>testtrygrep echo "" >>testtrygrep # --- 8< --- CUT HERE --- 8< --- CUT HERE --- 8< --- CUT HERE --- 8< --- # # and run patch tool # patch -b RunGrepTest RunGrepTest.fix
2. You need LibreSSL
(special thanks go to: http://www.gctv.ne.jp/~yokota/clamav/). I was always using OpenSSL, but recently I had more and more issues with it while compiling stuff from sources.
cd $HOME/opt/src curl -O https://ftp.openbsd.org/pub/OpenBSD/LibreSSL/libressl-2.6.4.tar.gz tar zxf libressl-2.6.4.tar.gz cd libressl-2.6.4 export CXXFLAGS="-O3" export CFLAGS="-O3" ./configure --prefix=$HOME/opt/usr/local/libressl make make check make install
3. You need zlib
cd $HOME/opt/src curl -O http://zlib.net/zlib-1.2.11.tar.xz tar zxf zlib-1.2.11.tar.xz cd zlib-1.2.11 ./configure --prefix=$HOME/opt/usr/local/zlib make make install
4. Build the stuff
cd $HOME/opt/src git clone git://github.com/vrtadmin/clamav-devel cd clamav-devel git checkout tags/clamav-0.100.0 -b rel/0.100 # you can also get stable version from here: # https://www.clamav.net/downloads export CFLAGS="-O3 -march=nocona" export CXXFLAGS="-O3 -march=nocona" export CPPFLAGS="-I$HOME/opt/usr/local/pcre2/include \ -I$HOME/opt/usr/local/libressl/include \ -I$HOME/opt/usr/local/zlib/include" ./configure --prefix=$HOME/opt/usr/local/clamav --build=x86_64-apple-darwin`uname -r` \ --with-pcre=$HOME/opt/usr/local/pcre2 \ --with-openssl=$HOME/opt/usr/local/libressl \ --with-zlib=$HOME/opt/usr/local/zlib \ --disable-zlib-vcheck \ make make install
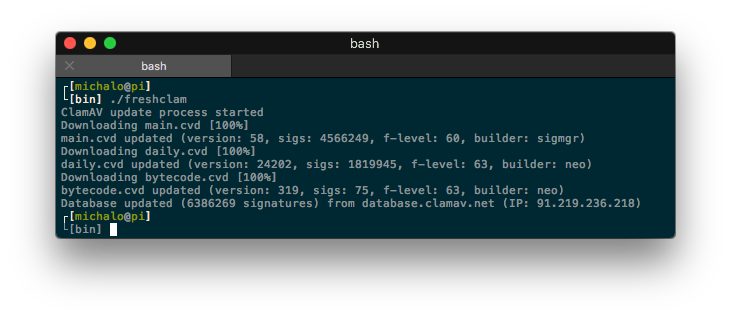
5. Make sure to keep your database up to date
$HOME/opt/usr/local/clamav/bin/freshclam
6. Now, you can scan your drive for viruses
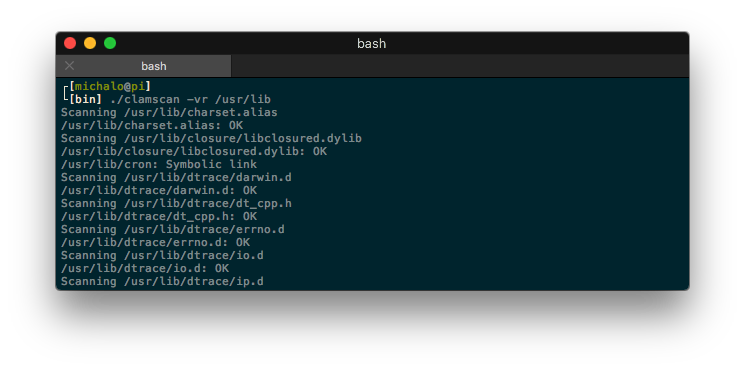
cd $HOME $HOME/opt/usr/local/clamav/bin/clamscan --log=$HOME/scan.log -ir $HOME # if you want to scan your whole drive you need to run the thing as root # I also suggest to exclude /Volumes, unless you want to scan your TimeMachine # and all discs attached # -i - report only infected files # -r - recursive # --log=$FILE - store output inside $FILE # --exclude=$DIR - don't scan directory $DIR cd $HOME sudo $HOME/opt/usr/local/clamav/bin/clamscan --log=`pwd`/scan.log --exclude=/Volumes --exclude=/tmp -ir /
To compile ClamAV on macOS High Sierra I have used my old scripts, but many thanks go to: http://www.gctv.ne.jp/~yokota/clamav